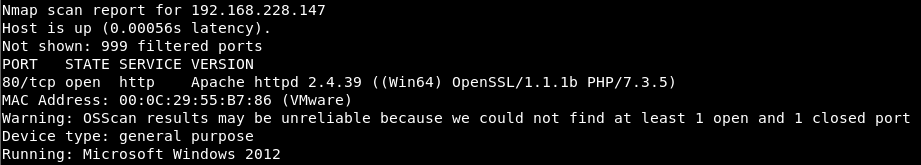
This article describes the solution steps of the retired machine ‘’ICECREAM’’ on the PriviaHub platform. First of all, scanning has been started to detect the open ports on the machine, current services running on the open ports and operating system. For the scanning process, Nmap has been used and nmap -A <<IP_Address>> -Pn -v command has been executed. -A parameter is a parameter that performs SYN scan, current service version scan, operating system scan and traceroute scan. -Pn parameter is used to scan machines that are closed to PING request.
Because nmap performs a PING scan by default and if the system does not accept ping requests, nmap does not perform any scan to the system and decides that the system is offline. This is because the machines on the PriviaHub platform are inspired by real company networks and many machines on the PriviaHub platform are closed to PING. -v parameter is also used to give detailed information.
As a result of the scanning process, it was found that port 80 is open, “Apache 2.4.39” service is running on this port and operating system is the “Windows Server 2012”.
Access to the web application running on the Apache service is provided through the web browser via port 80.
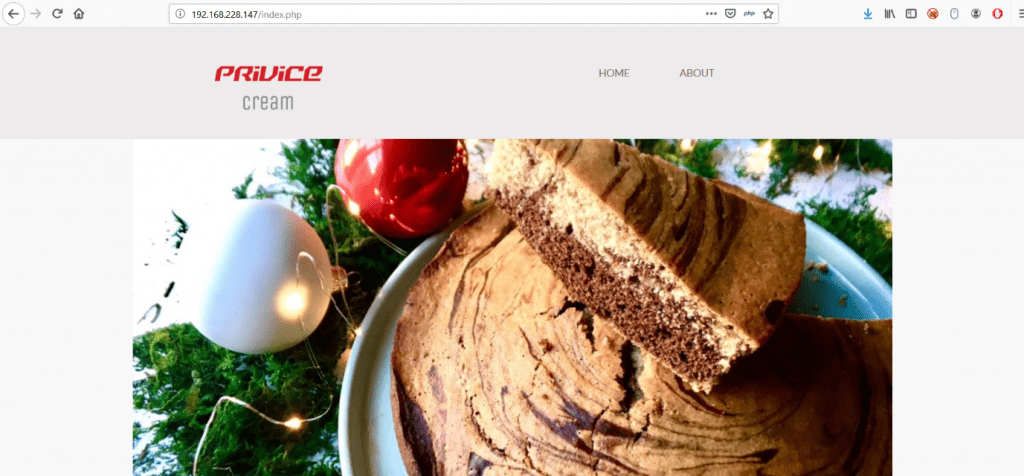
When the “ABOUT” page is accessed via home page, to display content of this page, the path to the page is assigned to a parameter named “file”.
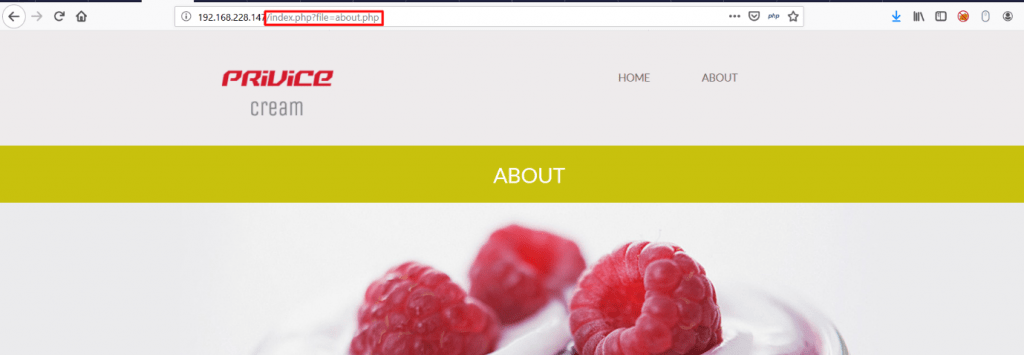
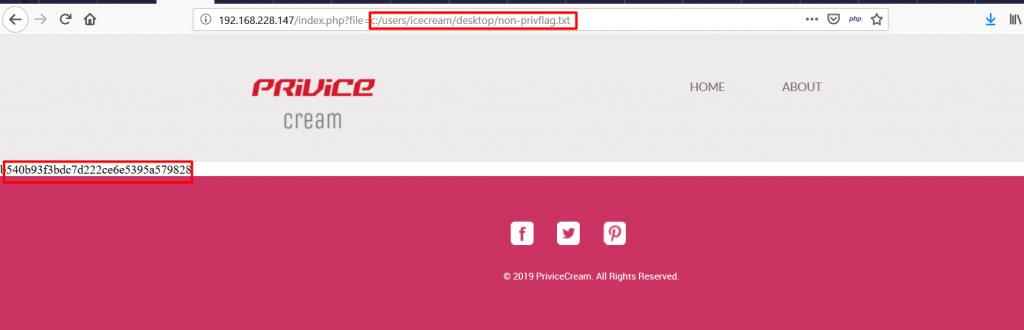
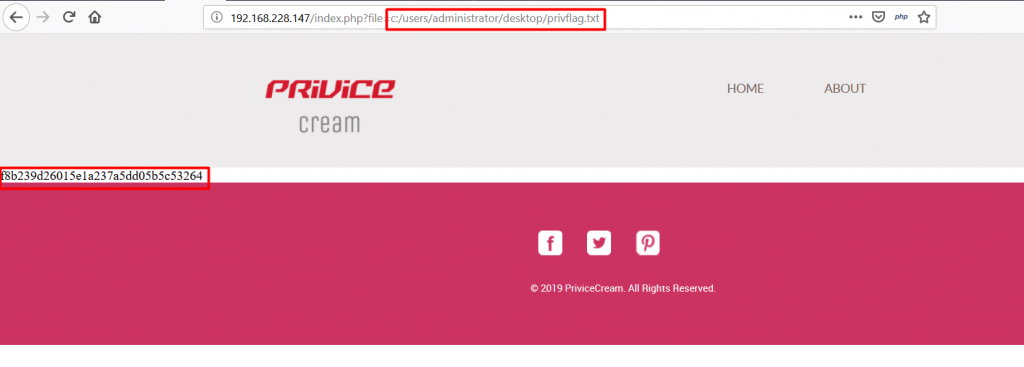
This assignment takes advantage of the “include()” function of the PHP programming language and the content of all local files to be assigned to the “file” parameter is added to the content of the page named “index.php”. This causes the LFI (Local File Inclusion) vulnerability.
For test purposes, the content of the file named win.ini was successfully displayed by specifying the path “C: \Windows\win.ini”.
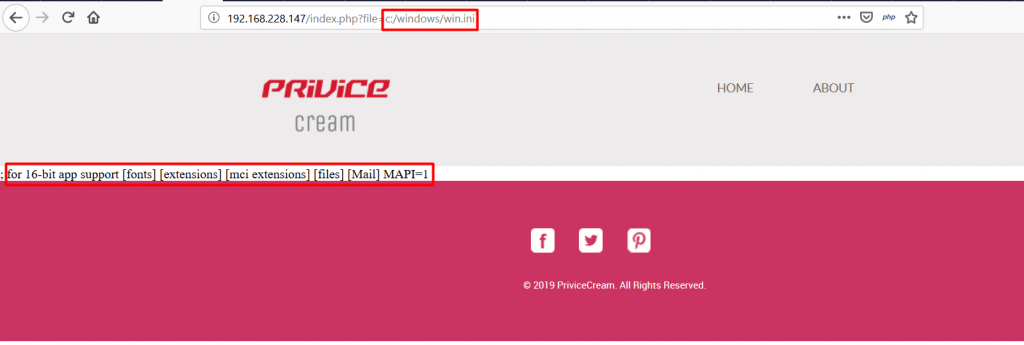
Then, by exploiting the LFI vulnerability, the paths where the flags are located are assigned to the “file” parameter and the flags are displayed on the index.php page.