The importance of a robust Cyber Security framework for any private or governmental entity, relying heavily on Cyber Space and digital technologies for its operations, cannot be over emphasized in this technology dominated era . No civilian or military organization can consider itself secure in the Cyber domain without a comprehensive and dynamic Cyber Security Strategy involving an integrated implementation of technical, procedural, and human elements of its digital environment. While organizations continue to employ innovative methods and techniques to counter the burgeoning Cyber threats, there are always procedural loopholes, technical vulnerabilities and experience shortfalls that remain undetected. These undetected vulnerabilities and loopholes are often exploited by the Cyber criminals to compromise sensitive data and often result in the suspension of critical operations. These security breaches could not only mean huge financial and reputational losses for the companies but can also become serious national security issues for the governments. According to Statista, the worldwide cost of Cybercrimes has seen an exponential increase from 0.7 trillion dollars in 2007 to 7.08 trillion dollars per Anum in 2023. This figure is expected to reach a whooping 13.82 trillion dollars by 2028; that would be world’s third biggest economy after the US and China.
These serious financial and national security concerns have forced private and public sector institutions to accord the highest priority to Cyber Security and spend huge amounts of money on ensuring security of their operations in the Cyber Space. While Cyber Security companies continue to provide innovative security solutions, Cyber criminals and rogue elements generally retain the initiative in the Cyber War equation; a phenomenon which is likely to continue into the foreseeable future. This fact was emphasized by one of the computer pioneers Mr Willis Ware, who famously remarked that “the only completely secure computer is a computer that no one can use.” Hence, Cyber domain shall always remain under threat till the time we continue to rely on it. The rising trend of Cyber Crimes and incidents worldwide, indicates that Cyber Security incidents and breaches can only be prevented and their losses minimized but they cannot be possibly eliminated. So, in such a complex, challenging, vulnerable and unpredictable digital environment, how to prevent Cyber Security breaches and minimize damages? The answer lies in adapting the concept of Cyber Wargaming where the latest technologies and Cyber Security techniques are employed in an integrated manner to avoid surprises and minimize damages. Cyber Wargaming if conducted regularly and professionally with the right technical tools and experienced staff, can tremendously help institutions strengthen their Cyber Security Posture and avoid costly surprises by timely plugging-in the usually undetected technical and procedural loopholes and vulnerabilities and preparing for unexpected situations.
Cyber Wargaming – Learning from Military
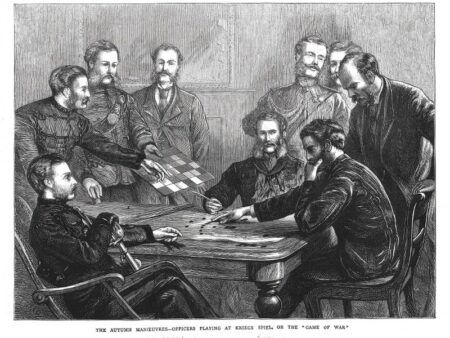
The concept of formal war-gaming was first introduced by a Prussian officer Lieutenant Georg von Reiswitz in early 19th century when he convinced his seniors that war could be re-created and exercised on a map to simulate different scenarios. Since then militaries around the world rely on war-games to minimize surprises and avoid catastrophic failures by taking uncertainties into account to identify areas of potential risk, and to employ planning tools, like scenarios, to narrow the range of uncertainty where possible. Wargames are tabletop or simulation-based analytic games/exercises that simulate aspects of warfare between opposing forces at the tactical, operational, or strategic level. They are used to examine warfighting concepts, train and educate commanders and analysts, explore scenarios, and assess how force planning and posture choices affect campaign outcomes. Militaries undertake various types of wargames, including scenario exercises, tabletop map exercises, and computer-supported exercises. They also provide opportunities to test strategies/concepts, train professionals, find out weak areas/shortcomings, test weapons, verify procedures, prepare response strategies and help in strategic decision making. Depending on their scale and scope, war-games also help in bringing together inter/intra agency stakeholders to build relationships and work together towards a common cause which may lead to developing a unique solution to a complex problem; a solution that can be beneficial for all the allies and partners.

Practice of the War-Gaming concept in the Cyber world is comparatively a new phenomenon which needs to take roots for delivering the maximum benefits. Although many militaries around the world understand the possible national security implications of Cyber threats and are therefore regularly undertaking Cyber Wargames at national level and with Allies, Cyber Wargaming in the private/civilian sector is still in infancy.

Cyber wargames differ from traditional Cyber Security measures like evaluating technology controls, pen-testing and vulnerability scans etc. Cyber wargames not only encompass these traditional Cyber Security measures (when required) but also provide a wholesome assessment of an organization’s Cyber Security Posture / strategy by bringing a near-realistic experience of Cyber Warfare to life. Cyber war games also prepare companies and organizations for streamlining the decision making processes in unexpected situations where they may have to shut down part of a corporate network and mitigate losses. Hence, Cyber Wargames not only help in identifying technical vulnerabilities but are an excellent tool for evaluating your cyber security strategy, response mechanisms, professional competence, decision making processes in a crises situation and enabling you to withstand unexpected situations in the event of a Cyber Attack.
Designing a Cyber Wargame
Designing and supervised conduct of a Cyber Wargame is a complex process that must be undertaken with the help of experienced and competent professionals utilizing the right technical tools. Since Cyber Wargames are designed to provide a near real-time experience to the participants, designers of the wargame must be familiar with the latest attack and defense techniques and technologies. Businesses,, companies or organizations can also undertake Cyber Wargames at their own provided they have the right kind of technical infrastructure, trained human resource, and maturity level. However, if any of these elements is missing or is considered inadequate, it is better to take help of qualified professionals and outsource wargaming where external experts. It is also important to understand that it is not only the technical experts who take part in a full fledge Cyber Wargame. The key stakeholders or the
C-Suite of the company or the institutions must be fully involved to play their decision making role while different scenarios or contingencies are presented during the course of the exercise. Also, involvement of a company’s legal, HR, support and administrative staff, as well as the PR teams to practice real time decisions and actions shall also play a vital role in determining the overall outcome of the wargame.
The first step in designing a Cyber Wargame is to gain clarity on the scope and objectives of the wargame. Comprehensive understanding of the digital environment of an organization or company including its vital digital assets/services facilitates planners in designing a realistic Wargame.
Scope of the Cyber Wargame
Defining the scope and scale of the wargame is a prerequisite for further planning and conduct. Scope of the wargame can range from testing tactical to operational or strategic level of the Cyber Security posture of an organization/institution besides providing near real-time experience/training to the cyber security professionals. The number and level of participants are determined by the scope and scale of the wargame. Similarly, the exercise can span over days to weeks or months depending upon the desired outcomes and objectives set forth. It is important to understand the level of competence of the participants before defining the scope and scale of a wargame as it has direct implications on the outcome of the exercise. Special precautions and mitigation measures are to be kept in place if the exercise is planned to be conducted on live-systems to avoid unexpected disruption in the operations.
Safest option to undertake a Cyber Wargame in a near-realistic environment is to have the exercise conducted on a potent Cyber Range Platform which has the capabilities to replicate multiple digital environments including organizational environment encompassing its networks, systems and associated operational services to provide a near real-time experience. A comprehensive Cyber Range Platform enables you to create a wider scope for the exercise without worrying about the interference with the live-systems and networks.
PriviaHub is an online Cyber Security Training, Simulation and Exercise (Cyber Range) Platform that enables personnel working in private or public institutions to increase their level of knowledge and make practical applications.
Defining objectives of the Cyber Wargame
After finalizing the scope of the wargame, it becomes easier to set forth the objectives of the wargame. Objectives can range from tactical to operational or strategic level depending upon the scope of the exercise. Since a Cyber Wargame is much more than simple pen-testing, it must encompass a wider range of objectives to yield real dividends. Generally, some of the objectives that can be set forth for a Cyber Wargame, include:-
- Testing the overall Cyber Security posture/strategy of an organization or institution
- Finding out technical vulnerabilities that can result in data loss or disruption of operations (Pen-testing/vulnerability scans etc)
- Evaluation of professional competence of Cyber Security professionals
- Testing response strategies and mechanisms – crisis management
- Educating/training the cyber professionals on latest defensive and offensive techniques and technologies
- Testing different hypotheses and scenarios
- Evaluation of the efficacy of existing procedures and protocols
- Testing new controls or procedures
- Building inter/intra agency relationships and improving communications
- Exploring solutions to complex problems/challenges
- Undertaking inter/intra agency exercises to evaluate Cyber Security preparedness of the institutions
- To draw pertinent lessons to improve upon the existing Cyber Security norms, technological know-how/availability, professional competence and SOPs
Organizations planning the Cyber Wargames may devise many other objectives as per their specific operational requirements and organizational dictates. It is always better to name the game to create a realistic effect and for documenting the post exercise lessons and conduct details. The planners of the exercise may choose a suitable name for the Wargame in consultation with the key stakeholders of the company.
Developing Scenarios
After laying down the scope and objectives of the intended Cyber Wargame, the designers/planners must develop scenarios replicating the most and least probable Cyber Security situations. The scenarios must provide ample opportunity to the participants of practicing and achieving the desired objectives of the wargame. Wargame scenarios may incorporate both planned and unplanned situations/events to generate a perfect-storm situation for the participants to face and handle the worst possible situations. Scenarios can be from testing the technical aspects of the latest attack/defense techniques to evaluation of the response strategies, professional competences and procedural efficacy. For example, what if there is an attack on the organizational network, or its data center is brought down, sensitive voice calls between the higher echelon are compromised (man-in-the-middle attack), a DDoS attack takes down the email server of the institution or there has been a serious Ransomware attack. Similarly, there can be a number of other situations that can be created during the scenario development phase depending upon the objectives of the Wargame. Planners of the Cyber Wargame must incorporate safety measures and cut-off thresholds in case the exercise is planned on the live systems. However, as highlighted earlier, it is always better to conduct large scale Cyber Wargames on a strong Cyber Range Platform. Good Cyber Range Platforms also have inbuilt scenarios related to the technical difficulty level with the capacity to create more with the available tools. However, situational scenarios aimed at evaluating response strategies and SOPs have to be created by the planners.
During this phase, planners in consultation with the relevant organization decide on how the exercise shall be conducted, what networks, systems, protocols, policies etc are to be replicated if the exercise is planned utilizing a Cyber Range Platform. Also, rules of the game, team/individual responsibilities (as per NIST Special Publication (SP) 800-61 Revision 2 (Rev. 2), cut-off thresholds, command and control and exercise conduct time-table are discussed and finalized. Constitution of the teams (Red, Blue, Purple, Control etc) depending upon the scope and objectives of the Wargame is also finalized during this phase.
Creating and Documenting Wargame Instructions – Briefing
Once the scope, objectives and scenarios/conduct methodology of the Cyber Wargame have been finalized, it is time for planners to prepare the document usually named as “Exercise Instructions” in detail which should include written scope, objectives, participants & teams, exercise conduct methodology, responsibilities of the teams and key stakeholders including the “Control”, “Referee” or “Facilitator”of the exercise. The document may or may not contain details of the scenarios depending upon the scope of the exercise. “Exercise Instructions” are to be vetted by the Chief Planner and key stakeholders of the company or organization for which the exercise is being conducted. This document can then be shared with the participants to understand various aspects of the Wargame and to give them time for preparation. Exercise preparations also include ensuring availability of the technical infrastructure, systems, facilities and admin support required for the Wargame. Finally, after adequate time has been given to the participants and key stakeholders to understand Wargame instructions, a final briefing is to be conducted before the start of the Wargame. Main objective of this central briefing is to refresh the conduct methodology and to clarify any questions that might have arisen in the minds of the participants.
Conduct of the Cyber Wargame
The Wargame conduct is governed strictly by the “Exercise Instructions” to ensure a smooth and rewarding experience for all and to draw pertinent lessons. Depending on the objectives set forth for the exercise, both Red and Blue teams undertake offensive and defensive
cyber-attack activities where Red Team tries to compromise the Blue Team’s networks, systems, and services etc while the Blue Team identifies incoming attacks to defend or mitigate the damages. The “Control” or “Referee” of the exercise closely monitor the ongoing activities to ensure that everyone is following the rules laid down in the instructions. During the Wargames conducted on a typical Cyber Range, , a company’s live digital environment is simulated/replicated to provide near real-time feel for the participants and accrue realistic results. The Cyber Wargames can also be conducted on a pre-configured digital environment which is totally different from the company’s environment and unknown to both blue and red teams. In such exercise settings, the blue team has to discern the environment and associated systems to figure out how to protect before the red teams initiate attacks. Similarly, the “Control” or “Referee” or “Facilitator” can also present the teams with various scenarios designed to evaluate organization’s decision making and response strategies. It basically the “Control” who keeps everyone involved in the exercise on the same page. Procedural scenarios are exercised by giving a limited amount of time to the team taking actions and then its response actions and decisions are evaluated. Decisions and responses of the key stakeholders, HR, legal, PR and investor relations teams are documented and evaluated for their positive or negative impact on company’s operations, interests and public image.
The most important step during the conduct of a Cyber Wargame is to ensure auditable logging of the chains of evidence, incidents and contingencies as the exercise progresses. Likewise, a detailed record of the sequence of events including what was experienced at what time, were the exercise instructions followed, how well did the response strategy perform, were the key decision makers available in time to take critical decisions during contingencies, was the required information available on time and was the communication and coordination between different entities of the organization effective and timely. These technical and operational logs play a pivotal role in evaluating the wargame after its culmination and to draw correct lessons.
Concluding a Cyber Wargame
Once a Cyber Wargame has concluded, a clear message is to be conveyed to the participants by the “Control” to seize exercise activities. Now the process of collecting technical and operational logs from different teams and participants begins which must be undertaken meticulously to ensure integrity of the Wargame. “Control”, interacts with the key participants to gather all the relevant information and prepares a comprehensive “Post Wargame Report” which gives a detailed account of the exercise from its planning to conduct, culmination, lessons learnt and evaluates it keeping in view the scope and objectives of the Wargame. This report must cover all the positive and negative aspects related to the exercise including strengths and weaknesses of the organization in technical, professional competence and procedural effectiveness domains. NIST SP 800-61 Rev. 2 also provides elaborate guidelines for documenting “lessons learnt” during the exercise. The post wargame report should elaborate on all major incidents that were faced during the exercise including specifics like :-
- Details of the technical vulnerabilities and technical loopholes identified during the Wargame. What additional tools or resources are needed to detect, analyze and mitigate future incidents?
- Did organizational Response Strategy perform to handle various critical situations or is there a need of revisiting it?
- Were the competency levels of participants good enough at the company/organization to thwart Cyber threats?
- Were the steps or actions taken during contingencies enough?
- How well did staff and management perform in dealing with different incidents?
- What would the staff and management do differently the next time a similar incident occurs?
- Suggested future course of action for the company to improve upon its Cyber Security Posture.
Once the post wargame report has been finalized, a debrief session must be arranged by the planners of the wargame involving all stakeholders, participants and C-Suite of the company to share and discuss the report contents especially the lessons learnt during the wargame.
Conclusion Threats in the Cyber Domain continue to evolve and multiply with every passing day and it has become extremely challenging for private and public institutions to wrest the initiative from cyber criminals and rogue elements. Cyber security companies around the world are spending huge amounts of money on R&D to ensure that world continues to operate securely in the Cyber domain, however, cyber crime and cyber attacks from known and unknown entities continue to see an exponential rise around the globe; a trend which is likely to continue into the foreseeable future. While various organizations and institutions do undertake regular pen-tests, vulnerably scans and other technical measures to identify weak areas, there are always loopholes and vulnerabilities that go unnoticed/undetected and are later exploited by cyber criminals and rogue elements. In order to avoid surprises an integrated implementation of technical, procedural, and human elements of the digital environment of an organization to carve out a wholistic Cyber Security Strategy is the need of the time. Such an integrated Cyber Security Strategy can be distilled through the concept of Cyber Wargaming; a time-tested concept by the militaries around the world. Adapting the salient of military wargaming and implementing them in the Cyber Domain can tremendously help organizations/institutions in strengthening their Cyber Security Posture and avoid costly surprises by timely plugging-in the usually undetected technical and procedural loopholes and vulnerabilities while preparing them for unexpected situations. A potent and comprehensive Cyber Range Platform can be an ideal solution to undertake Cyber Wargaming and improve your Cyber Security Posture.
Writer: Nasim Abbas